CYBERMINDR USE CASE

Your security is only as strong as your weakest vendor. With over 60% of breaches tied to third-party failures, CISOs and GRC teams can no longer rely on questionnaires or point-in-time assessments. They need continuous, evidence-driven visibility.
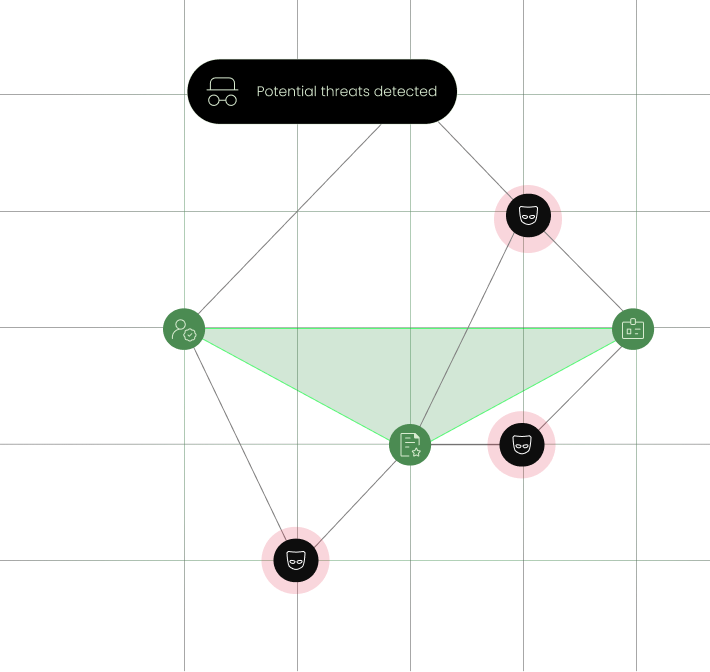
CyberMindr delivers a unified, real-time view of your entire vendor ecosystem, showing exactly what attackers can see, analyze, and exploit, before it becomes your risk.
See your vendor exposures in real time
Book a Demo

Dynamic Vendor Footprint

Delayed Notifications

Scattered Visibility

Self- attested Risk

Point-in-time Monitoring


You don’t need separate tools. CyberMindr consolidates the essentials into a single, continuous view.

Your vendor landscape is never static. CyberMindr ensures your visibility isn’t either.

Track third-party risk and your own organization’s threat exposure in the same platform, creating a unified view across your digital ecosystem.

Findings are correlated with external intelligence and risk categories that matter.

Every finding includes technical detail and contextual relevance, making it easier to present to auditors, executives, and partners.

Instant vendor posture snapshots speed up onboarding and reduce reliance on lengthy questionnaires.
CyberMindr transforms TPRM from a periodic “checklist activity” into a continuous, assurance model powered by real signals.
Map each vendor’s externally visible digital footprint—domains, subdomains, tech stacks, IP ranges, open ports, and misconfigurations. CyberMindr continuously enriches this footprint to ensure nothing goes unnoticed.
Track risk changes across vendors in real time. CyberMindr assigns a category-based vendor risk score using verified external signals and optional permitted validation.
Detect leaked credentials, botnet indicators, ransomware leaks, and publicly exposed code tied to vendors. Every leak includes attribution and context for rapid remediation.
Monitor SSL/TLS issues, HTTPS enforcement, DNS weaknesses, subdomain takeovers, and unsafe ports, highlighting misconfigurations that elevate vendor risk.
Match vendor assets to dark-web chatter, impersonation domains, blacklists, and threat-actor activity, flagging issues earlier than traditional tools.
Where right-to-audit exists, CyberMindr performs controlled validation to confirm exploitability of high-impact vulnerabilities.
A single, unified dashboard to visualize, track, and manage your entire vendor ecosystem.




Focus on validated external exposures, simulated attack paths and remediation workflows.

Get instant vendor risk snapshots, standard clauses, pre-contract review support.

Audit-ready reports, continuous monitoring, supply-chain risk assurance.
CyberMindr is not limited to a vendor-risk solution. It is your central command center for:
Threat intelligence
Your organization’s attack surface
Third-party risk
Credential & identity exposures
DNS & infrastructure hygiene
Brand impersonation detection
Subsidiary and shadow-IT visibility

Stay Ahead of Vendor
Risk
Gain visibility and control to secure your digital ecosystem with confidence.
See your vendor risk posture live, in under 30 minutes.