The Rise & Fall of Attack Surface Management (ASM)


The birth of the Internet marked the beginning of a new era, leading to a rapid increase of always-connected software and machines. As this digital realm evolved, so did the realization of its inherent threats and bad actors, prompting the need for new and specialized security measures. The concept of an “external attack surface” emerged, representing the points or vectors from which unauthorized users or attackers could target an environment, from the outside via the internet.
Over the last three decades, the ‘global attack surface’ has dramatically expanded, transitioning from simply keeping track of on premises systems, ports and protocols to worrying about things such as online code repositories, cloud hosted assets, data on the dark web and more. This evolution in the threat landscape underscores the critical necessity for monitoring and managing these attack surfaces.
One solution that has emerged in recent years is Attack Surface Management tools or ASM. Since an Attack Surface represents both inside and outside the firewall issues, some people will refer to external solutions such as External Attack Surface Management or EASM.
Current (E)ASM solutions represent an evolution in a variety of methods and technologies that evolved with the growth of both the internet and data gathering methods.
In the early 2000s, what we now call the Google Hacking Database (GHDB) started as Google Dorks, an index of search queries used to find publicly available information. Thousands of unsecured, remotely accessible security cameras and printers could still be discovered through simple Google searches.
Founded by a group of volunteers, Shadow server became a primary source for security researchers in 2004. It operates on the principle that sharing Internet Attack Data enhances overall security.
In 2009, John Matherly indexed Internet service banners across the net, providing the data at ShodanHQ, known today as the Google of network services.
2012 witnessed the release of the Internet Census, an audacious but illegal project that scanned the entire IPv4 address space using a botnet.
Following this, Zmap and Masscan, both lightning-fast port scanners, were introduced.
Today, search engines like Shodan.io and Censys.io enable anyone to scan the Internet and collect active and passive reconnaissance results for open services and devices. However, these tools are limited to identifying exposed digital assets.
Recognizing the need to move beyond merely identifying vulnerabilities, security professionals developed Attack Surface Management tools. These tools could discover, analyze, prioritize, remediate and monitor various entry points that cybercriminals might exploit to gain unauthorized access to an organization’s network or assets.
As the attack surface continues to expand, the demand for ASM grows. However, the traditional approach of addressing individual security threats falters in the face of evolving technologies such as mobile, cloud, IoT and their associated threat vectors.
The journey of ASM through the years has been marked by milestones and innovations. However, recent surveys reveal a sobering reality challenge that bring us to the crossroads of ASM’s effectiveness. Let’s delve into the current state of ASM and the pressing issues it grapples with.
In a recent survey, 29% of companies admitted overpaying for their ASM platform, while a substantial 50.9% expressed dissatisfaction with their current ASM platform’s capability to identify previously unknown IT systems and applications.
For years, ASM has been a tool for discovering hidden assets and managing inventory. However, as external vulnerabilities continue to pose a growing risk of breach, organizations find that relying solely on ASM is no longer sufficient. Here’s why:
Acknowledging these challenges, organizations are realizing the shortcomings of traditional ASM. The future of ASM unfolds as organizations seek solutions beyond legacy approaches. Let’s explore the promising avenues reshaping the future of ASM.
Although not really ASM, there is a solution category that, on the surface, sounds like it attempts to address the same problems that ASM was built for. Security risk scoring solutions primarily operate external to the company and try to report on the state of your security.
Think of cyber risk scores like credit scores but designed specifically for online security or cybersecurity.
It shows how secure and vulnerable a company’s computer systems are to things like hacking, stealing information, or unauthorized access.
These scores are derived from passive data sources OSINT which monitors the use of strong passwords, the implementation of two-factor authentication, the use of encryption technology and more. The higher the score, the better protected the company is from cyber threats.
Companies generally use these scores to check how risky it might be to work with other companies or competitors. It is not used for their own security audits but to understand the risks associated with 3rd parties. By monitoring these scores over time, organizations make smart decisions about future investments and partnerships.
The traditional approach to Attack Surface Management (ASM) has become inadequate for the nuanced needs of modern organizations, particularly in the pursuit of contextual awareness. Security teams find themselves overwhelmed with threat intelligence data. Yet they struggle to gain the visibility required to safeguard their organization, infrastructure, and mission-critical digital assets effectively.
While ASM is still growing in its adoption, other solutions and processes are emerging to help address some of the limitations.
EASM is a comprehensive approach that utilizes technology, processes and services to safeguard critical digital assets from external threats, strengthening an organization’s cyber defenses. It ensures unparalleled visibility into servers, providing a holistic understanding of the digital landscape. The tool identifies and safeguards credentials, crucial for preventing unauthorized access and potential data breaches, and addresses public cloud service misconfigurations to prevent security loopholes.
Additionally, by identifying vulnerabilities in third-party software code, EASM fortifies against external threats, reducing the risk of data loss. Its emphasis on asset discovery contributes valuable information to the broader Cyber Asset Attack Surface Management (CAASM) process, enhancing the organization’s overall security posture.
However, EASM comes with its share of challenges. It heavily relies on external data sources, potentially leading to delays or incomplete threat intelligence. While excelling in external threat mitigation, EASM may have a limited focus on internal vulnerabilities. Implementing EASM can be complex, requiring meticulous configuration and integration efforts. The tool’s sensitivity may result in false positives, necessitating careful validation of identified threats. Moreover, EASM tools can be resource-intensive, impacting system performance and requiring efficient resource management.
In leveraging EASM, organizations must carefully weigh the advantages against these potential drawbacks.
As defined by Gartner in 2021, Cyber Asset Attack Surface Management (CAASM) is a robust solution addressing persistent challenges in asset visibility and vulnerability management, allowing organizations to navigate the complexities of the digital landscape effectively.
CAASM provides a comprehensive view of internal and external assets, enhancing insight through seamless API integrations with existing tools. The detailed mapping offered by CAASM facilitates the proactive identification and prompt remediation of security control gaps, offering a strategic understanding of an organization’s digital landscape.
However, CAASM presents challenges, including complex implementation requiring significant configuration efforts and resource-intensive tools impacting system performance. Sensitivity to false positives and a potential limited focus on emerging threats are additional considerations.
In the context of the evolving cyber landscape, the 2023 State of Cyber Assets Report reveals a notable 133% year-over-year growth in cyber assets for organizations. This surge resulted in a remarkable 589% increase in security vulnerabilities, underscoring the impact of doubling the number of assets.
While CAASM provides a strategic and comprehensive approach to asset visibility and vulnerability management, organizations must carefully weigh its complexities and potential limitations. Thorough evaluation and strategic deployment are essential for realizing the full benefits of CAASM.
Digital Risk Protection Services (DRPS) form a comprehensive solution delivered through a combination of technology and services, offering robust safeguarding for critical digital assets against external threats. It excels in providing unparalleled visibility into the open, dark, and deep web, supplying valuable context on threat actors and their tactics.
As a valuable addition to the cybersecurity toolkit, DRPS goes beyond traditional security measures by covering digital footprint and threat monitoring. This complements the focus on asset-based security risks addressed by Cyber Asset Attack Surface Management (CAASM) and External Attack Surface Management (EASM).
While DRPS provides extensive threat visibility and a contextual understanding of threat actors, organizations need to be mindful of potential drawbacks. Implementing DRPS tools may require substantial resources, impacting system performance. The comprehensive nature of DRPS may also lead to information overload, necessitating efficient data management strategies.
Continuous Threat Exposure Management (CTEM), envisioned by Gartner, signifies the future evolution of mature Attack Surface Management (ASM) tools. Incorporating CTEM into an organization’s cybersecurity strategy offers notable advantages. CTEM provides real-time monitoring capabilities, enabling prompt detection and response to emerging threats. Its proactive approach to vulnerability management ensures identification and mitigation of potential flaws before they can be exploited, enhancing overall cybersecurity resilience.
The strategic integration of CTEM with ASM tools further enhances the effectiveness of vulnerability management within an organization. CTEM stands out by surpassing traditional reactive measures such as firewalls and antivirus software. Instead, it adopts a proactive stance, actively seeking potential flaws and threats before exploitation.
As CTEM represents a forward-looking approach to vulnerability management, organizations can fully leverage the advantages of CTEM within their cybersecurity strategy.
Phase 3 of ASM, anticipated to commence around 2027, envisions ASM integrated into an automated security validation engine.
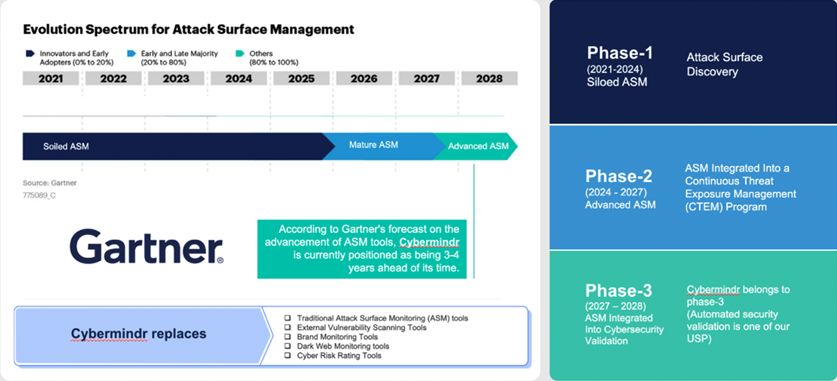
CyberMindr, a new-age CTEM platform falls into this category. It represents a leap towards more automated, proactive security measures.
As the cybersecurity landscape evolves, organizations are expected to embrace these advanced approaches to ensure a resilient defense against emerging threats and vulnerabilities. The future of ASM lies in its integration into broader cybersecurity strategies, emphasizing proactive and automated security practices.
Also see: Gartner Mentions CyberMindr in its Latest Preemptive Cybersecurity Strategies ReportAmidst the hourly exploits by Hacktivists, Cyber Criminals, and Nation-State Actors, Cybermindr offers a different approach—an outside-in view free from overwhelming false positives.
The platform focuses on validated vulnerabilities and confirmed attack paths, performing 15,000+ live checks on assets. It evolves with intelligence gathered from monitoring 300+ hacker forums, revealing attackers’ Tactics, Techniques, and Procedures (TTPs). This precision allows organizations to prioritize remediation efforts effectively.
In a landscape where not all ASMs are equal, businesses must expect more. Evaluate your ASM against organizational goals, emphasizing risk scoring to align with your executive risk management program.
Stay proactive—don’t let your attack surface outpace your ASM solution. Choose a platform seamlessly integrated with robust threat intelligence, automation, and risk-based vulnerability remediation. This strategic move will position your organization in the face of modern threats and challenges.